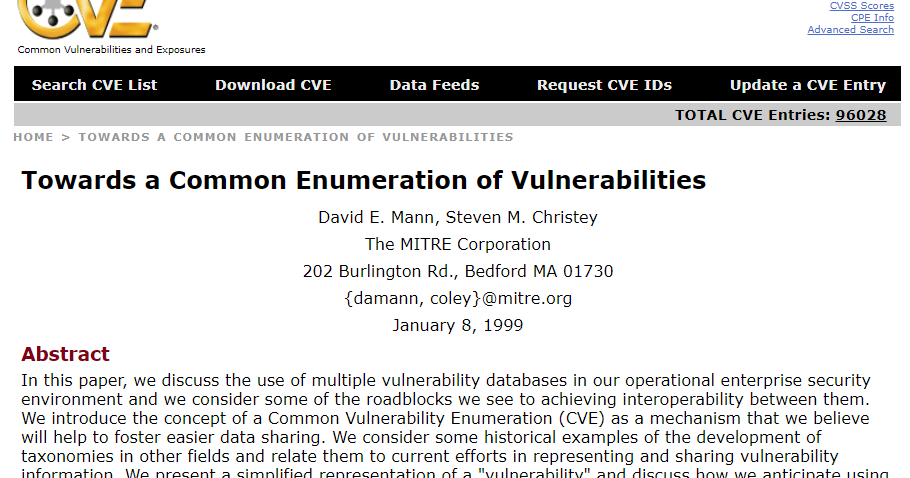
Adventures in Automation: Introduction to Vulns, Common Vulnerabilities and Exposures, the CVE List, and the National Vulnerability Database
![IPA Information-technology Promotion Agency, Japan : Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2017 3rd Quarter (Jul. - Sep.)] IPA Information-technology Promotion Agency, Japan : Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2017 3rd Quarter (Jul. - Sep.)]](https://www.ipa.go.jp/files/000062671.png)
IPA Information-technology Promotion Agency, Japan : Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2017 3rd Quarter (Jul. - Sep.)]