Teleportation scenario: Alice and Bob use a shared system in a quantum... | Download Scientific Diagram
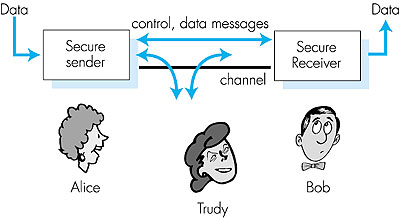
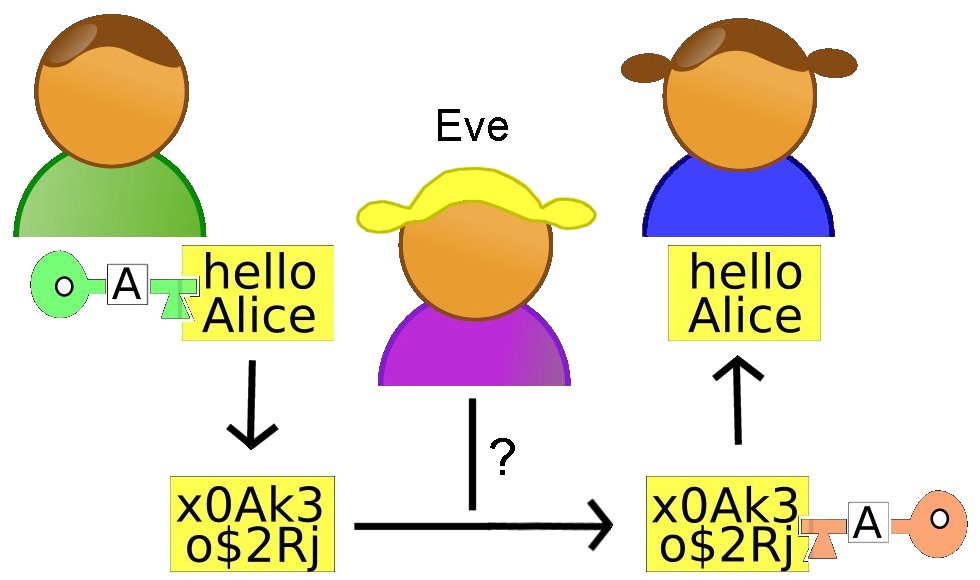
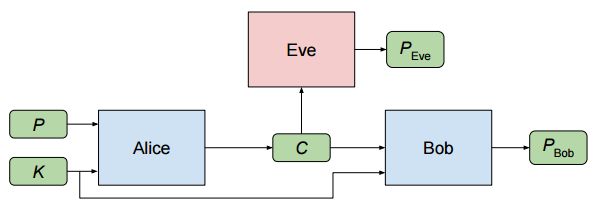
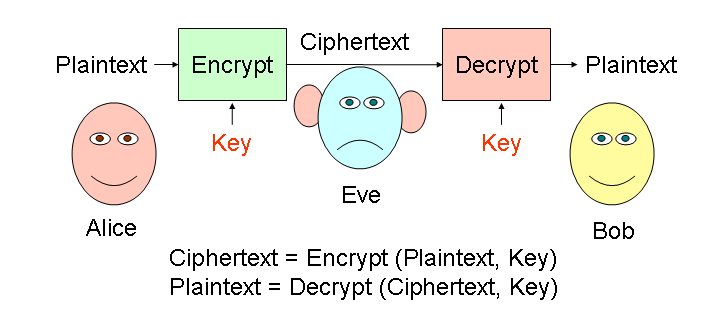
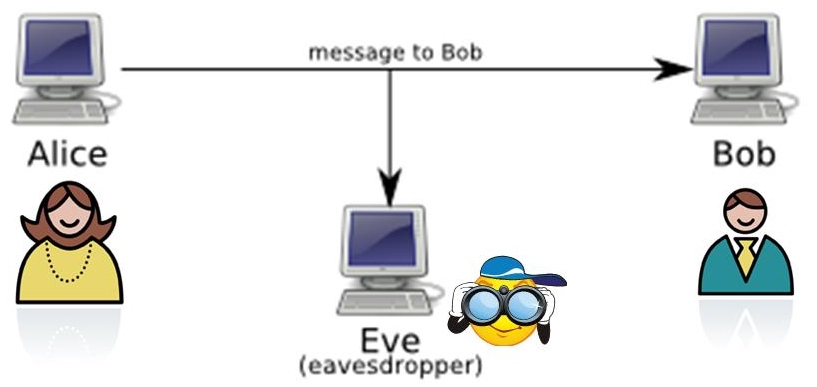
Computer Networking: A Top-Down Approach Featuring the Internet Chapter 8 -- 7.1: What is Network Security?

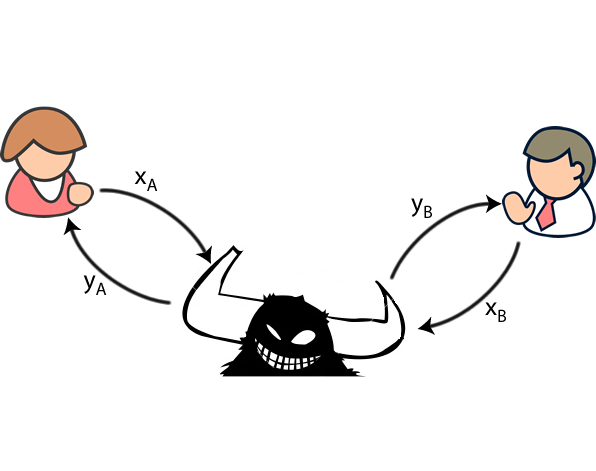
Communication Between Alice and Bob intercepted by Eve. Here channel is... | Download Scientific Diagram